Get the latest news delivered right to your email.
2024 Election
Top Stories
Advertisement
The New York Times Torches Biden for 'Troubling' Media Strategy in Official Statement
"It also establishes a dangerous precedent that future presidents can use to avoid scrutiny and accountability."
By Rachel M. Emmanuel
April 26, 2024
Comment
MoreShare
High School Student Who Refused to Remove US Flag from Truck Puts His Vehicle to Work, Drives Across Country for an Amazing Reason
The high school student who refused to remove the American flag from his truck used that same pickup to honor a boy's dying wish.
By Allison Anton
April 26, 2024
Comment
MoreShare
Columbia Slammed for Issuing 'Pathetic' Update on Anti-Israel Encampment
Columbia's approach to handling anti-Israel protests is making many furious as a deadline to end the protest has come and gone.
By Jack Davis
April 26, 2024
Comment
MoreShare
Nancy Pelosi Interrupted by Anti-Israel Protesters While Speaking Abroad - Security Does 'Nothing'
Nancy Pelosi criticized Israeli Prime Minister Benjamin Netanyahu in a speech, but that wasn't enough to appease protesters.
By Jack Davis
April 26, 2024
Comment
MoreShare
Former NFL Player Dies at Age 28
Cunningham was drafted in the seventh and final round of the 2018 NFL draft and he played for three teams during his career.
By Johnathan Jones
April 26, 2024
Comment
MoreShare
Democrats Run Focus Groups to Figure Out Why People Don't Like Kamala Harris and End Up Learning the Brutal Truth
"The bad news: Several people said Harris rubs them the wrong way, in all the ways that are familiar from criticism of her," CNN said.
By Connor Cavanaugh
April 26, 2024
Comment
MoreShare
Mitch McConnell Takes Public Shot at Tucker Carlson, Accuses Him of Turning Republicans Against Ukraine Aid
McConnell accused Carlson of turning Americans against Ukraine as the Senate prepares to vote on the most recent aid package.
By Anthony Altomari
April 26, 2024
Comment
MoreShare
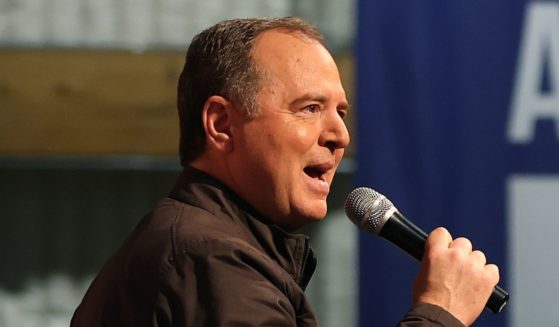
Adam Schiff Forced to Give Important Speech Without a Suit After California Thieves Steal His Clothes
Instead of attending a fundraiser in his usual suit and tie, Schiff wore a long-sleeve shirt and a hiking vest after his luggage was stolen.
By Johnathan Jones
April 26, 2024
Comment
MoreShare
Advertisement
Supreme Court Set to Decide Case That Could Criminalize Homeless Encampments
The U.S. Supreme Court heard oral arguments Monday regarding a case that could have major implications regarding homelessness in America.
Comment
MoreShare
Biden, Feds Possess Secret AI Tool to Censor and Indoctrinate 'At Scale' Ahead of Election - What You Need to Know
The House Judiciary Committee says there's an AI censorship program designed to skew the narrative toward the left before the 2024 election.
Comment
MoreShare
'Woman': The Left's Absurd Quest to Redefine the Term
The question “What is a woman?” is perfectly leveraged to produce absurdity because to pose this question is absurd.
Comment
MoreShare
Advertisement